-
We often receive DDoS attacks on our website. Could you please provide a tutorial on how to deploy it on Vercel?
-
@周林锋 DDoS attacks are typically mitigated at the ISP or Firewall level, and should not be actioned at the server level ideally - however, most of this depends on the type of DDoS attack.
For example, Layer 2 and 3 type attacks (Data and Network from the OSI Model) should always be handled by any traversing path other than the server itself - see below
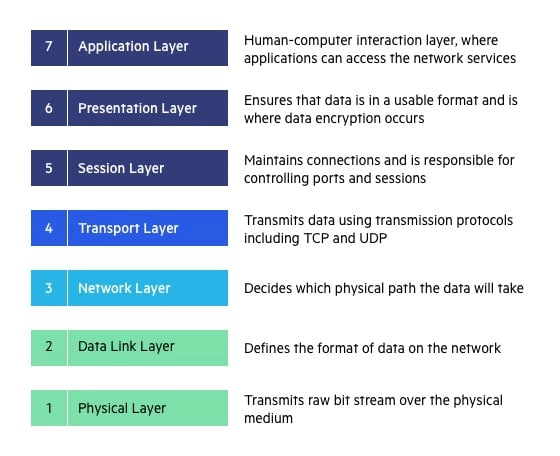
In this case, the ISP itself, or the firewall sitting in front of the server should have mitigation processes in place to prevent this type of attack hitting your server directly. Layer 7 attacks are different in their approach, and typically target the application directly. To avoid this, you should deploy a Web Application Firewall (WAF) that can filter out these types of attacks.
Essentially, the “easy” choice here is Cloudflare, although I note that your server is potentially located in China, so this may not be an option - although AWS (operated by Sinnet) is available - more information here
https://www.amazonaws.cn/en/new/2021/amazon-waf-available-china/
If you can provide more information around the infrastructure you have (not here, but via PM for security reasons), I can guide you further.
-
 undefined phenomlab moved this topic from Chitchat on
undefined phenomlab moved this topic from Chitchat on
-
No response from OP so marking as closed
Hello! It looks like you're interested in this conversation, but you don't have an account yet.
Getting fed up of having to scroll through the same posts each visit? When you register for an account, you'll always come back to exactly where you were before, and choose to be notified of new replies (either via email, or push notification). You'll also be able to save bookmarks and upvote posts to show your appreciation to other community members.
With your input, this post could be even better 💗
Register Login