Bad information security advice
-
It’s not often that I post anything on LinkedIn, but the post below caught my eye, and raised an eyebrow (to say the least) when I read it.
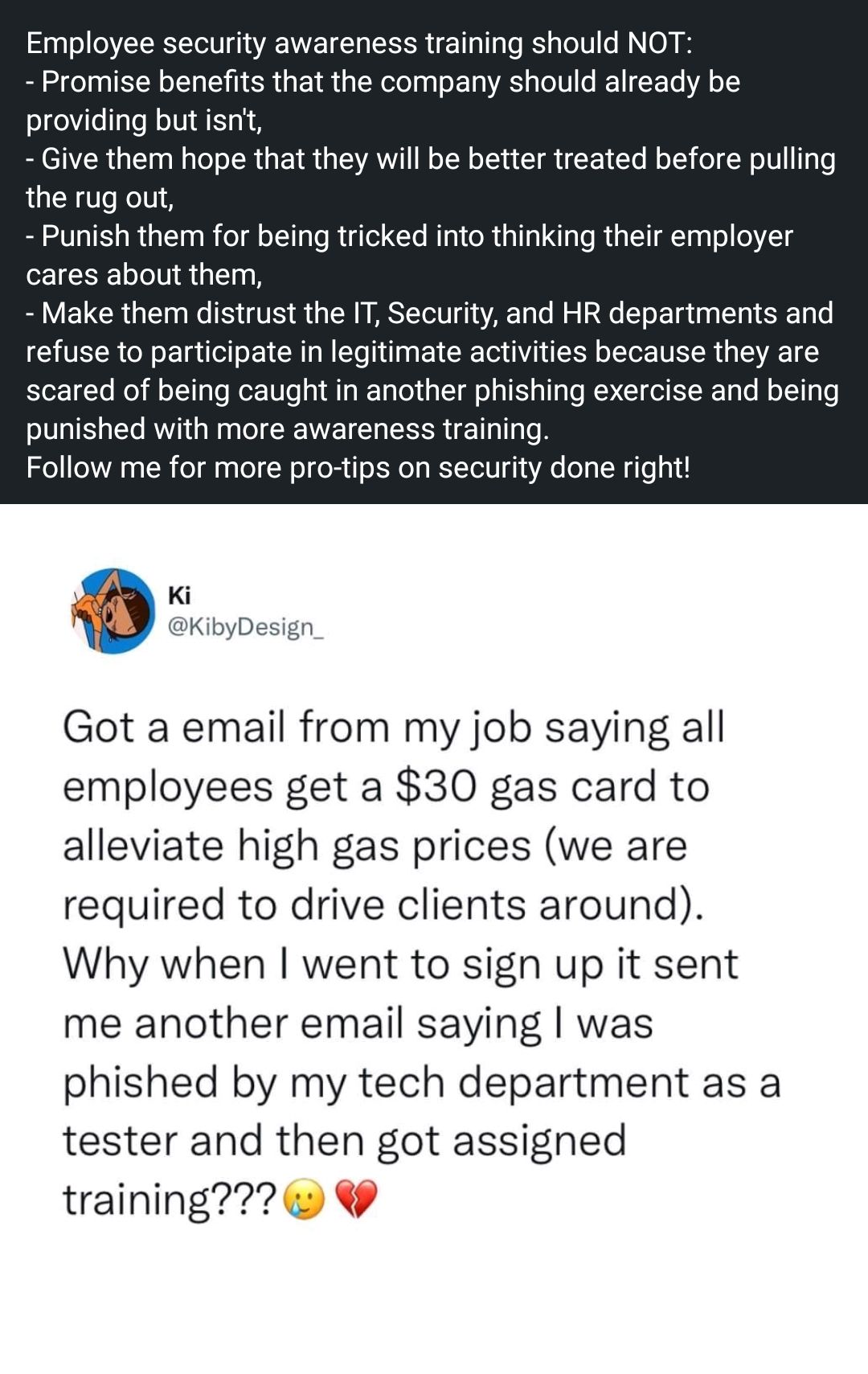
I typically remain impassive and neutral to most of these types of post as they are usually aimed at selling you something. However, the frankly absurd security advice here being offered was so bad, I found it hard to ignore and posted the below response
Forgive me if I decide not to take any of your cyber security advice as all of the points you’ve raised are the entire point of phishing exercises. Do you really think a nefarious actor isn’t going to send emails that look just like this (mostly because they have succeeded elsewhere as others have highlighted)?
Your profile states that you are the leader of a world class cyber security team, yet you offer really bad advice like this? This is exactly how all cyber security campaigns work and their effectiveness is blatantly obvious by the screenshot you posted.
“Hurt feelings” are irrelevant when you are measuring the effectiveness of your cyber security program. As the primary defense in any organization, the security department needs to be in a position to detect and repel as many attacks as possible. The paradigm here being that an organization needs to stop thousands of these attacks getting through per day (probably way more) yet an attacker only needs one link to be clicked for their campaign to succeed.
Employee security awareness should in fact be everything that the original poster claims it shouldn’t be. Just look at the success rate of previous campaigns which any decent training program is based on.
The bottom line here is that I really don’t understand the reasoning for the original post. This guy claims to be the leader of a world class cyber security team, yet he decides to give poor advice like this?
Speechless. And this is a so called professional?? We’re all doomed

Hello! It looks like you're interested in this conversation, but you don't have an account yet.
Getting fed up of having to scroll through the same posts each visit? When you register for an account, you'll always come back to exactly where you were before, and choose to be notified of new replies (either via email, or push notification). You'll also be able to save bookmarks and upvote posts to show your appreciation to other community members.
With your input, this post could be even better 💗
Register Login
