Setting for high load and prevent DDoS (sysctl, iptables, crowdsec or other)
-
Hello,
I am looking for ways to make the weavers that we top the world a little more secure via web servers etc…
I saw this article which allows to best configure the kernel:
https://www.thegeekdiary.com/sysctl-setting-for-high-load-and-prevent-ddos/
Do you think this config is valid @phenomlab or would you have others to offer?
I know Iptables can be a good tool too. I saw this article about it (but ideally for centOS, maybe it’s good for ubuntu server ?):
https://javapipe.com/blog/iptables-ddos-protection/
Using Virtualmin, if you have tricks for firewallD (installed by default), I’m interested.
Besides, FirewallD is based on its own app or on Iptables or something else like ufw?
I would be curious to know because I use it to open certain ports.
In short, a topic to list all the tips for securing a server and in this case a server without of course disturbing users accessing the web server and in this case, for me it is nodebb
cya
-
Hello,
I am looking for ways to make the weavers that we top the world a little more secure via web servers etc…
I saw this article which allows to best configure the kernel:
https://www.thegeekdiary.com/sysctl-setting-for-high-load-and-prevent-ddos/
Do you think this config is valid @phenomlab or would you have others to offer?
I know Iptables can be a good tool too. I saw this article about it (but ideally for centOS, maybe it’s good for ubuntu server ?):
https://javapipe.com/blog/iptables-ddos-protection/
Using Virtualmin, if you have tricks for firewallD (installed by default), I’m interested.
Besides, FirewallD is based on its own app or on Iptables or something else like ufw?
I would be curious to know because I use it to open certain ports.
In short, a topic to list all the tips for securing a server and in this case a server without of course disturbing users accessing the web server and in this case, for me it is nodebb
cya
@DownPW I’d steer well clear of modifying any kernel as detailed in the first post. There is so much that can go wrong here, it’ll take me a day to list all the possibilities. Whilst there’s nothing “wrong” with what is being suggested, it will affect the entire kernel and could present you with more issues than you set out to resolve.
You have to remember that what works for one person won’t work for another because every environment is different.
There’s also nothing fundamentally wrong with
FirewallDeither - it’s functional - albeit a bit basic, but it does the job very well and is simple to use. I’m curious to understand why you aren’t considering the Hetzner firewall as the first post as this makes much more sense to me in terms of handling DDoS traffic. -
Ha why not.
Because I just didn’t think of it lololI know hetzner has DDOS protection which works well unlike some provides.
It is active on my server but apart from 2 or 3 basic rules (SSH port, nodebb;) I don’t really see what to do with it
in short if you have any advice to give to secure the best.
-
Ha why not.
Because I just didn’t think of it lololI know hetzner has DDOS protection which works well unlike some provides.
It is active on my server but apart from 2 or 3 basic rules (SSH port, nodebb;) I don’t really see what to do with it
in short if you have any advice to give to secure the best.
@DownPW
 most of this really depends on your desired security model. In all cases with firewalls, less is always more, although it’s never as clear cut as that, and there are always bespoke ports you’ll need to open periodically.
most of this really depends on your desired security model. In all cases with firewalls, less is always more, although it’s never as clear cut as that, and there are always bespoke ports you’ll need to open periodically.Heztner’s DDoS protection is superior, and I know they have invested a lot of time, effort, and money into making it extremely effective. However, if you consider that the largest ever DDoS attack hit Cloudflare at 71m rps (and they were able to deflect it), and each attack can last anywhere between 8-24 hours which really depends on how determined the attacker(s) is/are, you can never be fully prepared - nor can you trace it’s true origin.
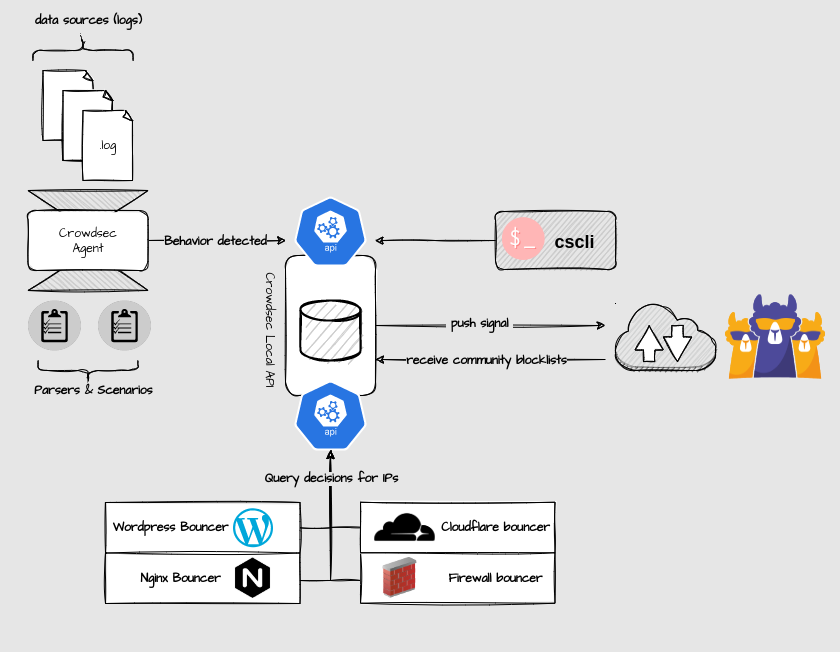
DDoS attacks by their nature (Distributed Denial of Service) are conducted by large numbers of devices whom have become part of a “bot army” - and in most cases, the owners of these devices are blissfully unaware that they have been attacked and are under command and control from a nefarious resource. Given that the attacks originate from multiple sources, this allows the real attacker to observe from a distance whilst concealing their own identity and origin in the process.
If you consider the desired effect of DDoS, it is not an attempt to access ports that are typically closed, but to flood (and eventually overwhelm) the target (such as a website) with millions of requests per second in an attempt to force it offline. Victims of DDoS attacks are often financial services for example, with either extortion or financial gain being the primary objective - in other words, pay for the originator to stop the attack.
It’s even possible to get DDoS as a service these days - with a credit card, a few clicks of a mouse and a target IP, you can have your own proxy campaign running in minutes which typically involves “booters” or “stressers” - see below for more
https://heimdalsecurity.com/blog/ddos-as-a-service-attacks-what-are-they-and-how-do-they-work
@DownPW said in Setting for high load and prevent DDoS (sysctl, iptables, crowdsec or other):
in short if you have any advice to give to secure the best.
It’s not just about DDos or firewalls. There are a number of vulnerabilities on all systems that if not patched, will expose that same system to exploit. One of my favourite online testers which does a lot more than most basic ones is below
https://www.immuniweb.com/websec/
I’d start with the findings reported here and use that to branch outwards.
-
 undefined phenomlab marked this topic as a regular topic on
undefined phenomlab marked this topic as a regular topic on
Hello! It looks like you're interested in this conversation, but you don't have an account yet.
Getting fed up of having to scroll through the same posts each visit? When you register for an account, you'll always come back to exactly where you were before, and choose to be notified of new replies (either via email, or push notification). You'll also be able to save bookmarks and upvote posts to show your appreciation to other community members.
With your input, this post could be even better 💗
Register LoginRelated Topics
-
-
-
-
-
-
-
-
SASL LOGIN authentication failed: generic failure
Moved Solved Linux