Arch Server Progress
-
@Madchatthew yes, it takes time, but no so much once you grow accustomed to the process. After a while you get a sense of what will work and what will not, and it also pays - certainly in the sense of PostFix to keep a golden configuration file that you know works.
It’s disturbingly easy to take PostFix offline with one single mistake.
@phenomlab yeah I have been reading about that as well in regard to Postfix. One little piece forgotten or changed in any little way can topple the whole thing down haha. It is crazy. And also, thank you for reminding me that once I get everything working and running to make a copy of those config files. That will help in the future and just may save my bacon.
-
I wanted to give an update on this. I have been working on trying to get a postfix, dovecot along with a couple of other programs working on this server. So far I have been unsuccessful. I am not giving up though and plan on starting a new thread to document each step that I take. Maybe someone will be able to see my mistake that I made or what I am missing and be able to help figure it out.
I know it would be easier to just go through one of the mail websites that are out there, but I would really like to learn this process.
-
I wanted to give an update on this. I have been working on trying to get a postfix, dovecot along with a couple of other programs working on this server. So far I have been unsuccessful. I am not giving up though and plan on starting a new thread to document each step that I take. Maybe someone will be able to see my mistake that I made or what I am missing and be able to help figure it out.
I know it would be easier to just go through one of the mail websites that are out there, but I would really like to learn this process.
@Madchatthew Feel free to post the issues here

-
Well, I must say that I was finally able to get email working on my Arch server. I still need to setup postgrey and some spam assassin, get the dmarc and spf and one or two others setup and then it should be good to go for the most part. I am mainly using it to be able to send mail from websites, but having the option to have a separate email for their domains will be very nice.
Once my brain solidifies after all of that, I will share what what I did. One thing I found is that it is important to just take it piece by piece and get each part working before moving on to the next. Also, test test test after each change, or each section.
-
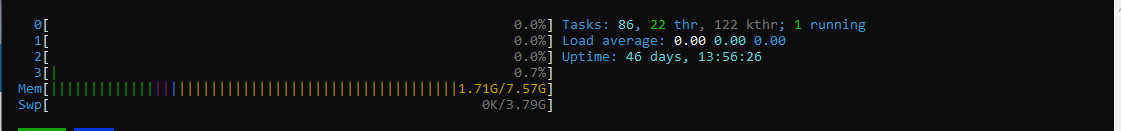
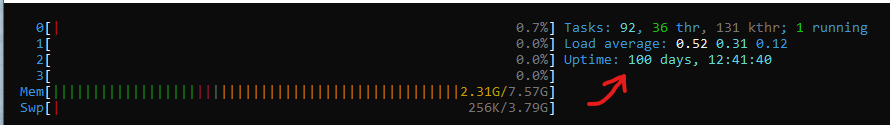
I also wanted to post this. Here are the latest stats for the server so far. This is with all of the software setup and running along with doing updates once a week after testing them on my dev test server and making sure websites function properly.
-
100 days up and running. I have been doing updates each week and websites running strong and fast. I do not regret my decision of switching to Arch.
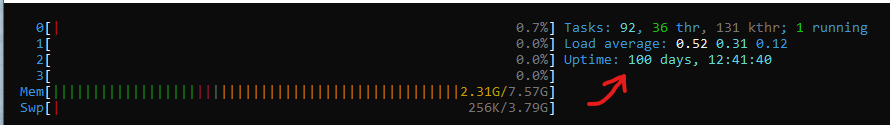
-
100 days up and running. I have been doing updates each week and websites running strong and fast. I do not regret my decision of switching to Arch.
@Madchatthew is this self hosted, or a VPS?
-
@Madchatthew is this self hosted, or a VPS?
@phenomlab It is a VPS on Hetzner.
-
So last week I updated my production server, so it had been two weeks since being updated due to being busy the week before and I didn’t have any issues after the upgrade. So far I haven’t had to restart this server and the websites are up and running very well. So I hope it stays that way.
-
So I was updating the server today and realized I didn’t have Reflector running on it. So I install that and set it up to run as a service. So my hope is that the mirrorlist will always stay updated so I won’t have the error pop up in case I were to miss a bunch of upgrades for some reason.
-
So my next project with the Arch Server is to get the email working properly on it. I actually do have it setup so I can set up the email account in an email client. The part I am having trouble with is setting up the email to be able to send from a WordPress site. I put in the information that I do for the email client and it just won’t send the email out. I also believe that it won’t send to a Gmail account so I think I have something not entered in correctly for the dmarc or the spf. So I need to figure that out, but once I do, I should have a fully functional email server that works for different applications.
-
So my next project with the Arch Server is to get the email working properly on it. I actually do have it setup so I can set up the email account in an email client. The part I am having trouble with is setting up the email to be able to send from a WordPress site. I put in the information that I do for the email client and it just won’t send the email out. I also believe that it won’t send to a Gmail account so I think I have something not entered in correctly for the dmarc or the spf. So I need to figure that out, but once I do, I should have a fully functional email server that works for different applications.
@Madchatthew Are you using Postfix for this in terms of the back-end?
-
@Madchatthew Are you using Postfix for this in terms of the back-end?
@phenomlab yes, postfix and dovecot.
-
So I am thinking maybe I need to do this with the config file and the functions file in the template to get the emailing from wordpress to work when submitting a form?
I am currently using WP SMTP Mail plugin, which I would think would configure all of this for me when I put in the information.
I also need to go back through this to make sure I set all this up correctly as well.
-
I was able to get the email server working appropriately this weekend. So now emails will be sent through to Gmail and such. I has to change the value of what was in my spf record, I added a dmarc and I already had a dkim entry in the DNS. I didn’t have to do anything to the dkim entry. I also had to point postfix to my SSL certificate of the server rather than the self signed one. Now I will be able to work on getting spam detection setup and virus scanning.
I was pretty happy when everything started working. I was able to do all of these changes without having to reboot the server. That is very nice so there was no down time. Of course using Debian or Ubuntu there is virtualmin that would have done all the configuration for me, but it was actually pretty fun getting things up and running and seeing all the interactions that are required on the backend. It is crazy everything that takes place that you don’t even realize when using the front end like virtualmin.
-
I was able to get the email server working appropriately this weekend. So now emails will be sent through to Gmail and such. I has to change the value of what was in my spf record, I added a dmarc and I already had a dkim entry in the DNS. I didn’t have to do anything to the dkim entry. I also had to point postfix to my SSL certificate of the server rather than the self signed one. Now I will be able to work on getting spam detection setup and virus scanning.
I was pretty happy when everything started working. I was able to do all of these changes without having to reboot the server. That is very nice so there was no down time. Of course using Debian or Ubuntu there is virtualmin that would have done all the configuration for me, but it was actually pretty fun getting things up and running and seeing all the interactions that are required on the backend. It is crazy everything that takes place that you don’t even realize when using the front end like virtualmin.
@Madchatthew said in Arch Server Progress:
Of course using Debian or Ubuntu there is virtualmin that would have done all the configuration for me, but it was actually pretty fun getting things up and running and seeing all the interactions that are required on the backend. It is crazy everything that takes place that you don’t even realize when using the front end like virtualmin.
Never a more true statement made. Virtualmin, whilst very convenient and “easy” (to a degree) often masks the real effort needed to get something working, and understanding what is “under the hood” is always better. When it breaks, you know where to look to fix.
-
@Madchatthew said in Arch Server Progress:
Of course using Debian or Ubuntu there is virtualmin that would have done all the configuration for me, but it was actually pretty fun getting things up and running and seeing all the interactions that are required on the backend. It is crazy everything that takes place that you don’t even realize when using the front end like virtualmin.
Never a more true statement made. Virtualmin, whilst very convenient and “easy” (to a degree) often masks the real effort needed to get something working, and understanding what is “under the hood” is always better. When it breaks, you know where to look to fix.
@phenomlab yes, and I never realized how in depth and how many processes it takes to manually do what Virtualmin does and I have a new found respect for everything that needs to happen for Virtualmin to make a virtual host and for everything to work.
-
@phenomlab yes, and I never realized how in depth and how many processes it takes to manually do what Virtualmin does and I have a new found respect for everything that needs to happen for Virtualmin to make a virtual host and for everything to work.
@Madchatthew it really is a great product - you cannot argue that.
-
@Madchatthew it really is a great product - you cannot argue that.
@phenomlab said in Arch Server Progress:
@Madchatthew it really is a great product - you cannot argue that.
100% agree!
-
So I have been battling the email server for a long time it feels like. I believe I have finally figured it out and what I needed to change to get it to work appropriately. I ended up having to change the server name and added mail.domain.com to it. I think I could have used anything, not just mail to get this to work. I could have used server1.domain.com or whatever word I wanted. This has to do with the reverse dns that you set in the settings for the server in the hosting companies dashboard. From my understanding, it seems to have something to do with how dmarc or dkim works. I can’t remember 100% off the top of my head right now. Then in the dns of the domain name, which is hosted on another site, i added mail.domain.com as an alias. All of those things point to the same IP, so I don’t think I would have had to add that with how things were set initially with domain.com.
I hope that makes sense. I then had to go into the server and change some of the configuration files for postfix, postfixadmin and change the domain.com entries to mail.domain.com and restart those services. Then I deleted the domains and mailboxes I created for postfix and recreated them. Then all of a sudden all of my test emails were delivered to the email addresses I created and to my gmail account. Now I just have to test the other email account I made and I should be good to go.
The awesome thing about changing the server name, is that I didn’t have to restart the server for it to take effect. You edit your
/etc/hostnamefile and type the name you want your server to be. Then you typehostnamectl set-hostname <new_hostname>and then in the console you can type inhostnamectland it will show the new hostname.
Hello! It looks like you're interested in this conversation, but you don't have an account yet.
Getting fed up of having to scroll through the same posts each visit? When you register for an account, you'll always come back to exactly where you were before, and choose to be notified of new replies (either via email, or push notification). You'll also be able to save bookmarks and upvote posts to show your appreciation to other community members.
With your input, this post could be even better 💗
Register Login