Windscribe VPN offered for free with a lifetime license
-
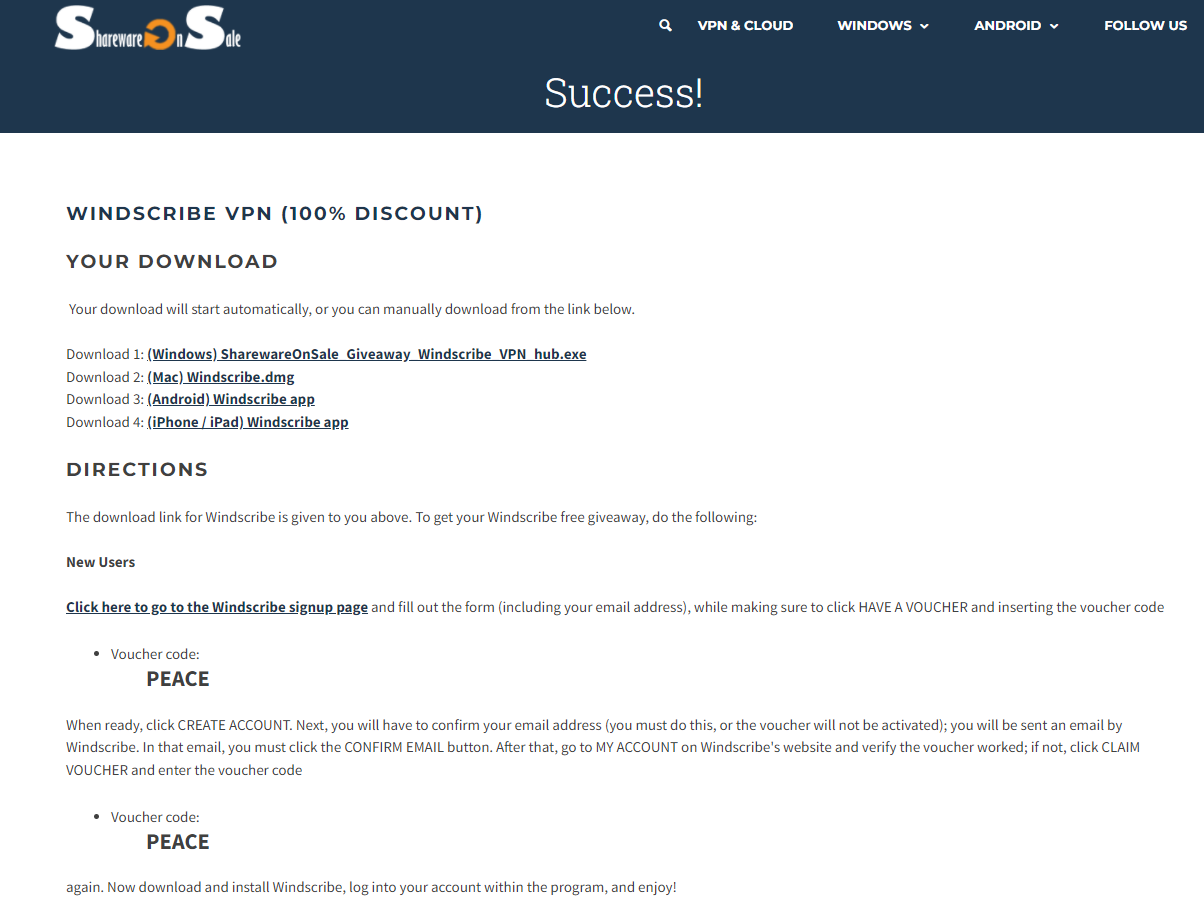
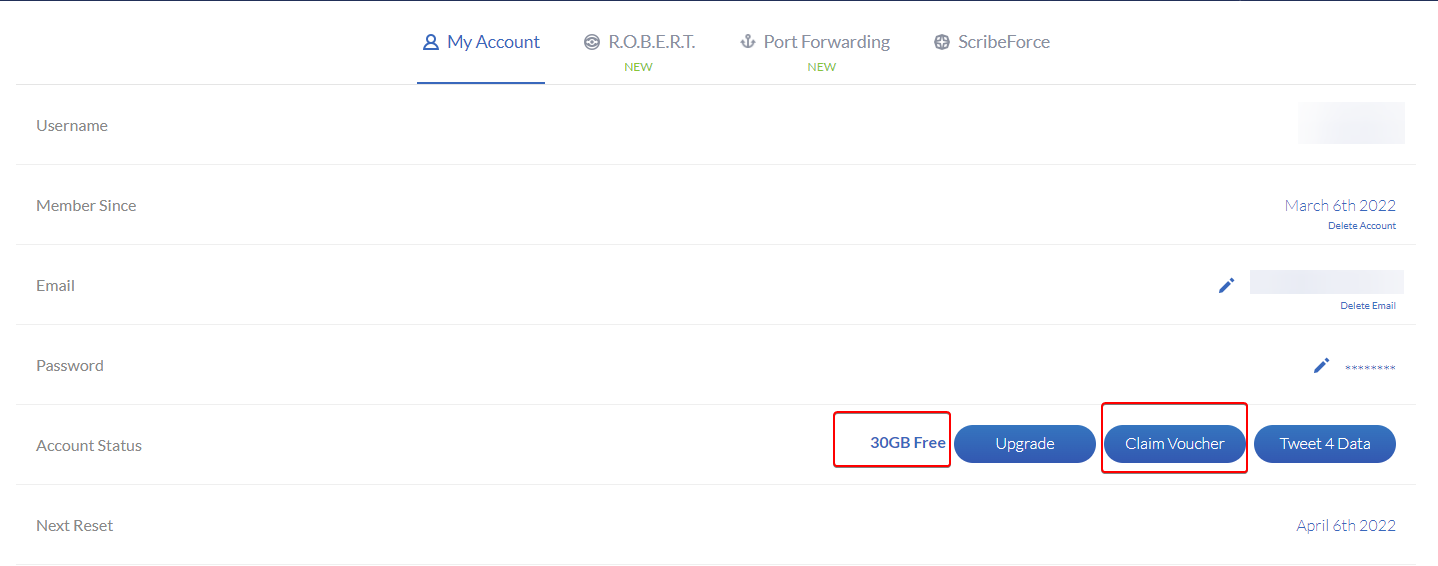
Windscribe VPN is currently offered for free with a lifetime license:
https://sharewareonsale.com/s/windscribe-vpn-giveaway-coupon-sale
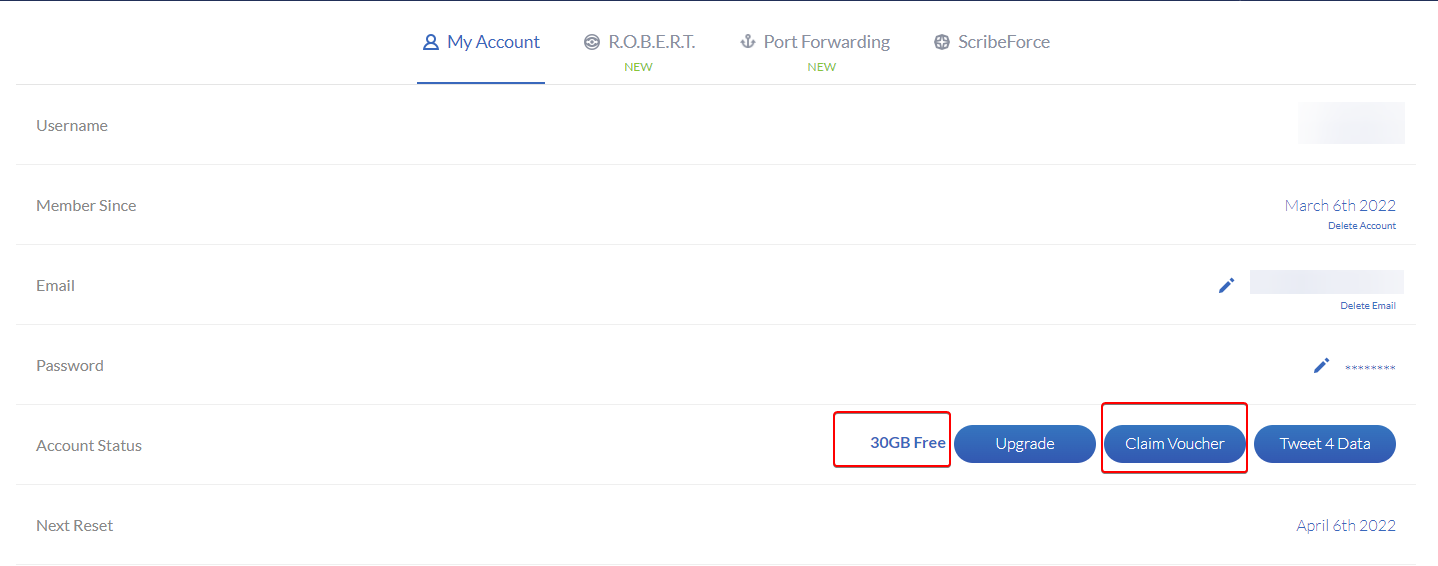
(30GB / month max for an unlimited number of devices)
It’s a VPN no-log, available under Windows, MacOS, Android, & iOS.
More info: https://windscribe.com/features
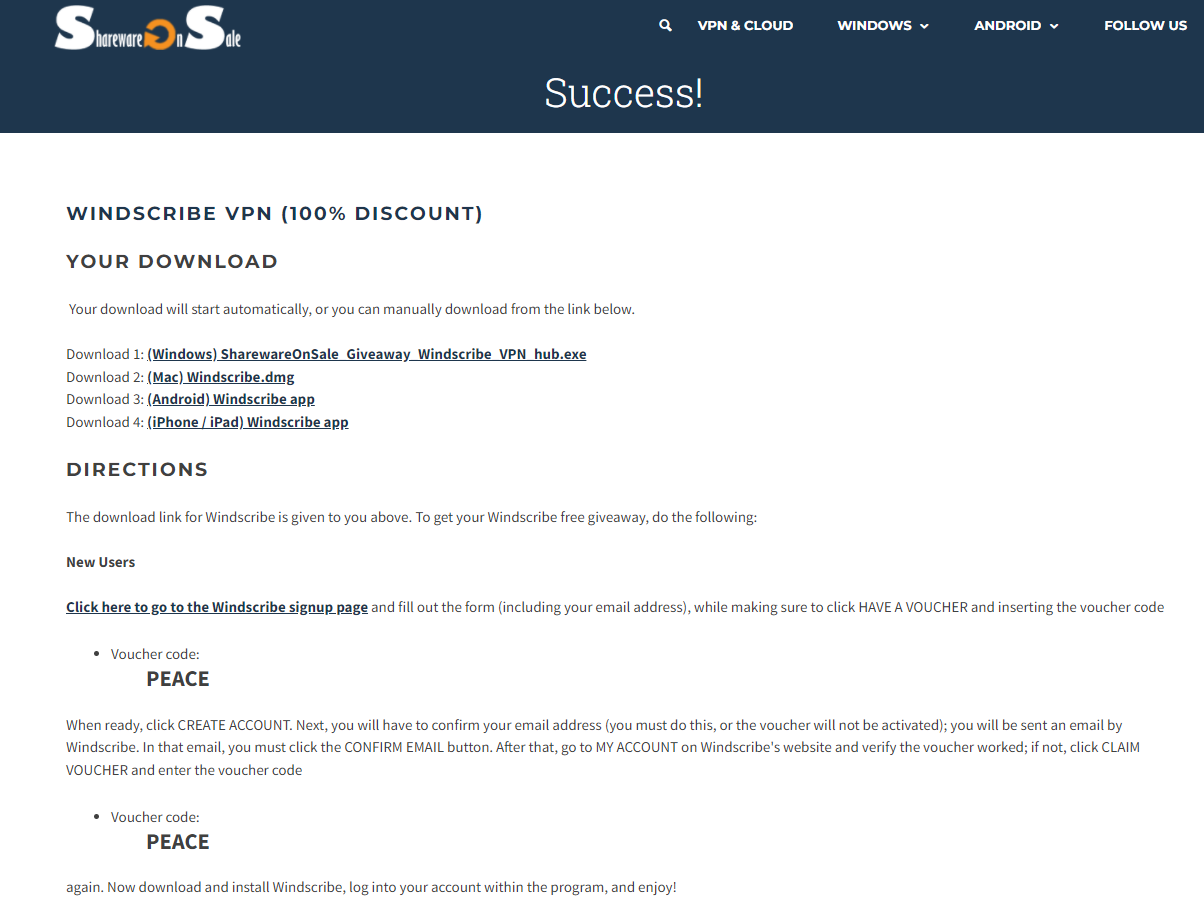
Promo code (voucher): PEACE
Registration link: https://windscribe.com/signup
-
Windscribe VPN is currently offered for free with a lifetime license:
https://sharewareonsale.com/s/windscribe-vpn-giveaway-coupon-sale
(30GB / month max for an unlimited number of devices)
It’s a VPN no-log, available under Windows, MacOS, Android, & iOS.
More info: https://windscribe.com/features
Promo code (voucher): PEACE
Registration link: https://windscribe.com/signup
@DownPW thanks for posting. Sadly not for Linux 🤬
-
arf yes…
Just android…For linux @phenomlab you can test ProtonVPN, the free edition is enough and it’s a very good VPN with good perf and security.
-
arf yes…
Just android…For linux @phenomlab you can test ProtonVPN, the free edition is enough and it’s a very good VPN with good perf and security.
@DownPW thanks. I actually have an active subscription to Nord VPN
-
@phenomlab said in Windscribe VPN offered for free with a lifetime license:
@DownPW thanks. I actually have an active subscription to Nord VPN
Enjoying Express VPN too, depending on what I’m using it for I do switch to Nord on occasions.
-
Missed out on this deal ? Windscribe offer a limited free version. More about that here
https://sudonix.org/topic/13/which-product-is-the-best-for-vpn/164?_=1652206628456
Hello! It looks like you're interested in this conversation, but you don't have an account yet.
Getting fed up of having to scroll through the same posts each visit? When you register for an account, you'll always come back to exactly where you were before, and choose to be notified of new replies (either via email, or push notification). You'll also be able to save bookmarks and upvote posts to show your appreciation to other community members.
With your input, this post could be even better 💗
Register Login