Network Security Monitoring
-
I am wondering what everyone is using for network security monitoring? I did a good search and there are so many options. I was also wondering if it is worth running a network monitoring software on a local network? Maybe it isn’t even worth running a tool like that on a local network? I don’t think people are trying to break into my local network, but was curious what others do.
Say I have virtual servers running that have the network card bridged. Is it worth having monitoring software installed and running for them as well?
-
I found this video that monitors all sorts of things over the network. Hardware and such as well. He goes over and how to setup Whats Up Gold. It is free for your personal network and for business it costs money of course.
Thoughts?
@phenomlab if you don’t want videos like this on your site let me know and I won’t do that for future posts. You can also remove the video from this post as well if not allowed.
-
I am wondering what everyone is using for network security monitoring? I did a good search and there are so many options. I was also wondering if it is worth running a network monitoring software on a local network? Maybe it isn’t even worth running a tool like that on a local network? I don’t think people are trying to break into my local network, but was curious what others do.
Say I have virtual servers running that have the network card bridged. Is it worth having monitoring software installed and running for them as well?
@Madchatthew certainly worth monitoring, but for it to work correctly, the bridge card needs to be running in promiscuous mode otherwise packets will be discarded by the NIC itself.
Are you looking specifically for security monitoring, or general performance monitoring also? I know that @DownPW has a lot of experience with Crowdstrike but that is essentially application layer rather than machine, so in the sense of the OSI model, it’s layer 7.
I suspect you are looking for layer 1 or 2 which would be physical (1) or data (2). There are numerous security products out there (some really good open source ones also) but I prefer to tap into the network stream at layer 3, so in this example, you’d use a network switch and create a network tap or mirroring port and use another program to read and analyse that traffic.
Taking this route means it’s agentless, and you don’t have to add machines manually. Really depends on what your requirements are.
-
I found this video that monitors all sorts of things over the network. Hardware and such as well. He goes over and how to setup Whats Up Gold. It is free for your personal network and for business it costs money of course.
Thoughts?
@phenomlab if you don’t want videos like this on your site let me know and I won’t do that for future posts. You can also remove the video from this post as well if not allowed.
@Madchatthew absolutely no issue. Including any source material such as videos is actively encouraged as it saves other members having to search themselves.
-
@Madchatthew certainly worth monitoring, but for it to work correctly, the bridge card needs to be running in promiscuous mode otherwise packets will be discarded by the NIC itself.
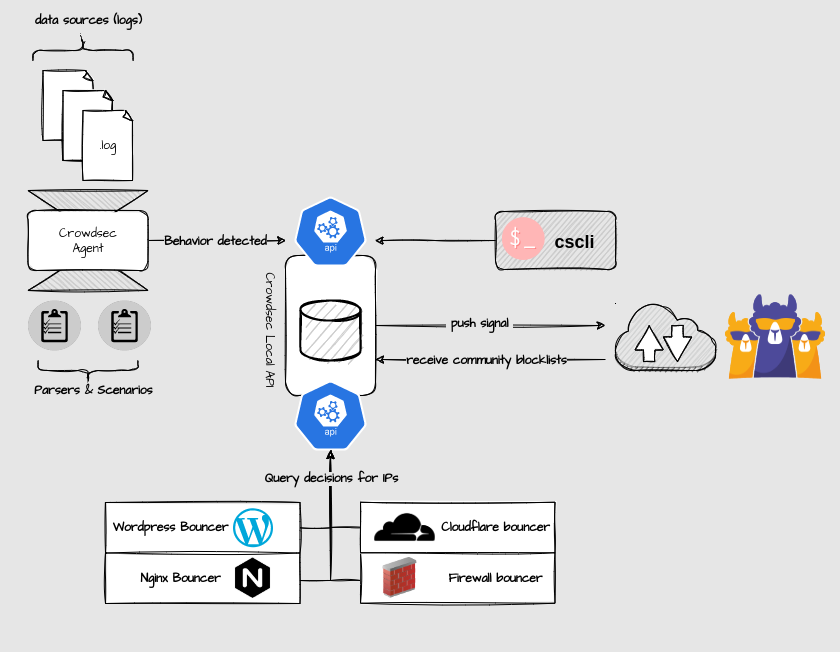
Are you looking specifically for security monitoring, or general performance monitoring also? I know that @DownPW has a lot of experience with Crowdstrike but that is essentially application layer rather than machine, so in the sense of the OSI model, it’s layer 7.
I suspect you are looking for layer 1 or 2 which would be physical (1) or data (2). There are numerous security products out there (some really good open source ones also) but I prefer to tap into the network stream at layer 3, so in this example, you’d use a network switch and create a network tap or mirroring port and use another program to read and analyse that traffic.
Taking this route means it’s agentless, and you don’t have to add machines manually. Really depends on what your requirements are.
@phenomlab To be honest, I didn’t really know what I am looking for or what level of monitoring I should do or if I even need to do any monitoring. I know with what seems like an increase in hacking lately, that maybe it wouldn’t be such a bad idea.
I do like the sound of layer 3 monitoring so you don’t have to manually add machines. Do you have some examples of some of the open source software out there that does the layer 1 or 2 monitoring?
@phenomlab said in Network Security Monitoring:
@Madchatthew absolutely no issue. Including any source material such as videos is actively encouraged as it saves other members having to search themselves.
Sounds good, thank you!
-
@phenomlab To be honest, I didn’t really know what I am looking for or what level of monitoring I should do or if I even need to do any monitoring. I know with what seems like an increase in hacking lately, that maybe it wouldn’t be such a bad idea.
I do like the sound of layer 3 monitoring so you don’t have to manually add machines. Do you have some examples of some of the open source software out there that does the layer 1 or 2 monitoring?
@phenomlab said in Network Security Monitoring:
@Madchatthew absolutely no issue. Including any source material such as videos is actively encouraged as it saves other members having to search themselves.
Sounds good, thank you!
@Madchatthew You could try this, but the hardware specs are insane.
https://github.com/telekom-security/tpotce
I’d couple this with Zabbix, which is an open source monitoring platform, but mostly geared towards operational monitoring rather than security.
For that, take a look at OSSEC
-
@Madchatthew You could try this, but the hardware specs are insane.
https://github.com/telekom-security/tpotce
I’d couple this with Zabbix, which is an open source monitoring platform, but mostly geared towards operational monitoring rather than security.
For that, take a look at OSSEC
@phenomlab I will check those out. Thanks for sharing. I appreciate it!
Hello! It looks like you're interested in this conversation, but you don't have an account yet.
Getting fed up of having to scroll through the same posts each visit? When you register for an account, you'll always come back to exactly where you were before, and choose to be notified of new replies (either via email, or push notification). You'll also be able to save bookmarks and upvote posts to show your appreciation to other community members.
With your input, this post could be even better 💗
Register Login