SSl expired on virtualmin
-
@phenomlab nothing happen
Ultimo rinnovo fallito 01/11/2022 1:09:26 PM
Rinnovo fallito a causa di Web-based validation failed :
Saving debug log to /var/log/letsencrypt/letsencrypt.log@justoverclock And if you try to request a new one ?
-
@justoverclock And if you try to request a new one ?
Saving debug log to /var/log/letsencrypt/letsencrypt.log
Plugins selected: Authenticator manual, Installer None
Renewing an existing certificate
An unexpected error occurred:
There were too many requests of a given type :: Error creating new order :: too many failed authorizations recently: see https://letsencrypt.org/docs/rate-limits/
Please see the logfiles in /var/log/letsencrypt for more details.so i need to wait hour? month?

-
Saving debug log to /var/log/letsencrypt/letsencrypt.log
Plugins selected: Authenticator manual, Installer None
Renewing an existing certificate
An unexpected error occurred:
There were too many requests of a given type :: Error creating new order :: too many failed authorizations recently: see https://letsencrypt.org/docs/rate-limits/
Please see the logfiles in /var/log/letsencrypt for more details.so i need to wait hour? month?

@justoverclock Yep, that’s the rate-limit message. Try again in an hour.
-
@justoverclock Yep, that’s the rate-limit message. Try again in an hour.
@phenomlab after one hour or more:
Saving debug log to /var/log/letsencrypt/letsencrypt.log Plugins selected: Authenticator manual, Installer None Renewing an existing certificate Performing the following challenges: dns-01 challenge for justoverclock.it dns-01 challenge for justoverclock.it Running manual-auth-hook command: /etc/webmin/webmin/letsencrypt-dns.pl Running manual-auth-hook command: /etc/webmin/webmin/letsencrypt-dns.pl Waiting for verification... Challenge failed for domain justoverclock.it Challenge failed for domain justoverclock.it dns-01 challenge for justoverclock.it dns-01 challenge for justoverclock.it Cleaning up challenges Running manual-cleanup-hook command: /etc/webmin/webmin/letsencrypt-cleanup.pl Running manual-cleanup-hook command: /etc/webmin/webmin/letsencrypt-cleanup.pl Some challenges have failed. IMPORTANT NOTES: - The following errors were reported by the server: Domain: justoverclock.it Type: dns Detail: DNS problem: NXDOMAIN looking up TXT for _acme-challenge.justoverclock.it - check that a DNS record exists for this domain Domain: justoverclock.it Type: dns Detail: DNS problem: NXDOMAIN looking up TXT for _acme-challenge.justoverclock.it - check that a DNS record exists for this domain -
@phenomlab after one hour or more:
Saving debug log to /var/log/letsencrypt/letsencrypt.log Plugins selected: Authenticator manual, Installer None Renewing an existing certificate Performing the following challenges: dns-01 challenge for justoverclock.it dns-01 challenge for justoverclock.it Running manual-auth-hook command: /etc/webmin/webmin/letsencrypt-dns.pl Running manual-auth-hook command: /etc/webmin/webmin/letsencrypt-dns.pl Waiting for verification... Challenge failed for domain justoverclock.it Challenge failed for domain justoverclock.it dns-01 challenge for justoverclock.it dns-01 challenge for justoverclock.it Cleaning up challenges Running manual-cleanup-hook command: /etc/webmin/webmin/letsencrypt-cleanup.pl Running manual-cleanup-hook command: /etc/webmin/webmin/letsencrypt-cleanup.pl Some challenges have failed. IMPORTANT NOTES: - The following errors were reported by the server: Domain: justoverclock.it Type: dns Detail: DNS problem: NXDOMAIN looking up TXT for _acme-challenge.justoverclock.it - check that a DNS record exists for this domain Domain: justoverclock.it Type: dns Detail: DNS problem: NXDOMAIN looking up TXT for _acme-challenge.justoverclock.it - check that a DNS record exists for this domain@justoverclock Seems your
_acme-challengeDNS record is missing ?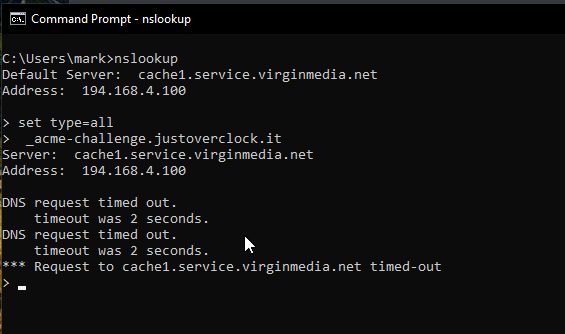
-
@justoverclock Seems your
_acme-challengeDNS record is missing ?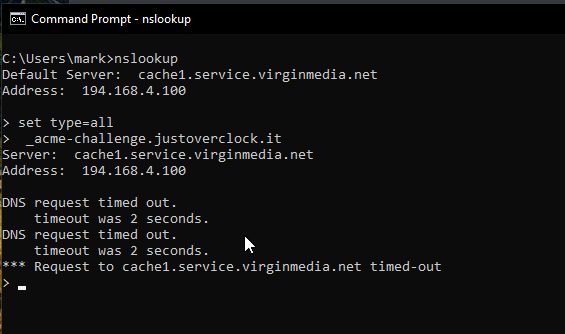
@phenomlab didn’t touch anything from your last visit

-
@phenomlab didn’t touch anything from your last visit

@justoverclock Very odd. Let me have a look at another way
-
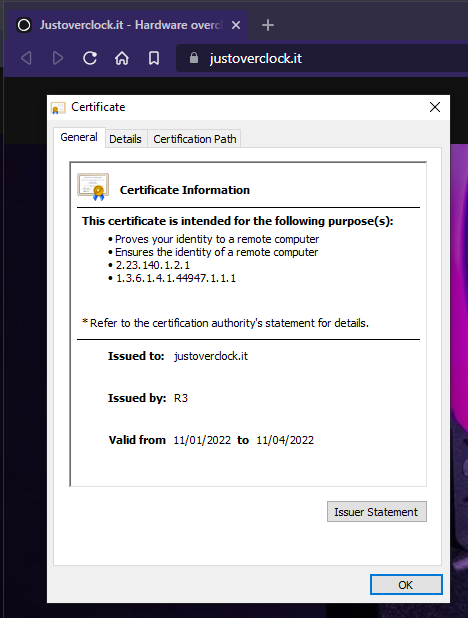
@justoverclock I have installed the
--nginxversion ofcertboton your server as per
https://sudonix.com/post/689It’s showing that the renewal will work, but the rate-limit is currently still enforced, so we still need to wait.
Performing the following challenges: http-01 challenge for justoverclock.it http-01 challenge for www.justoverclock.it Waiting for verification... Cleaning up challenges - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - new certificate deployed with reload of nginx server; fullchain is /etc/letsencrypt/live/justoverclock.it/fullchain.pem - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - ** DRY RUN: simulating 'certbot renew' close to cert expiry ** (The test certificates below have not been saved.) Congratulations, all renewals succeeded. The following certs have been renewed: /etc/letsencrypt/live/admin.justoverclock.it/fullchain.pem (success) /etc/letsencrypt/live/forum.justoverclock.it/fullchain.pem (success) /etc/letsencrypt/live/justoverclock.it/fullchain.pem (success) ** DRY RUN: simulating 'certbot renew' close to cert expiry ** (The test certificates above have not been saved.) - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - IMPORTANT NOTES: - Your account credentials have been saved in your Certbot configuration directory at /etc/letsencrypt. You should make a secure backup of this folder now. This configuration directory will also contain certificates and private keys obtained by Certbot so making regular backups of this folder is ideal. root@justoverclock:/home/justoverclock# -
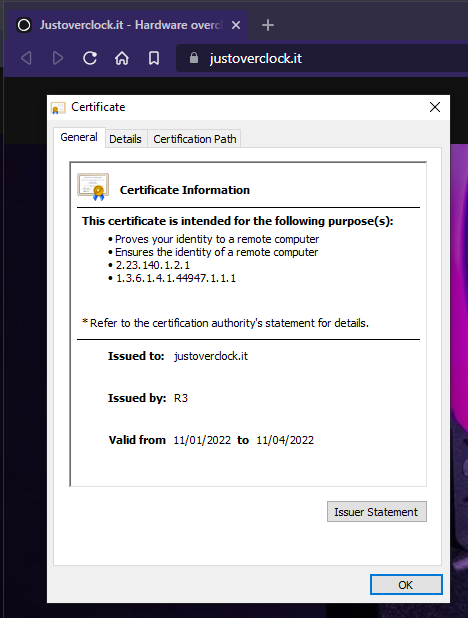
@justoverclock should be resolved now
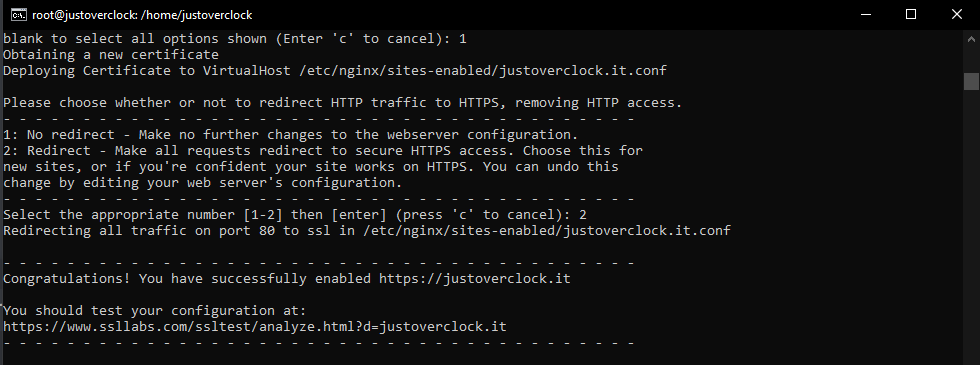
As a side note, this renewal won’t show in Virtualmin unless it is requested from there. This is done from the command line, so
- SSH into the server
- Change to root
- Execute
certbot --nginxand follow the prompts
-
 undefined phenomlab has marked this topic as solved on
undefined phenomlab has marked this topic as solved on
-
@justoverclock should be resolved now
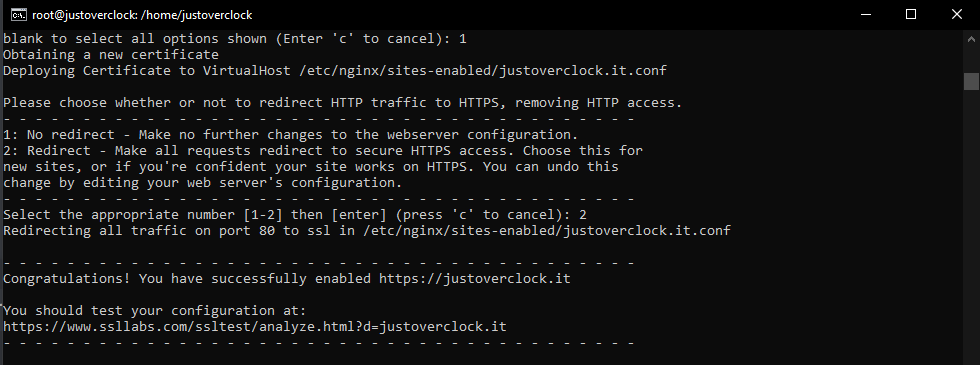
As a side note, this renewal won’t show in Virtualmin unless it is requested from there. This is done from the command line, so
- SSH into the server
- Change to root
- Execute
certbot --nginxand follow the prompts
@phenomlab so this is the command that i need to use everytime my certificate expire? thank you, precious as always
-
@phenomlab so this is the command that i need to use everytime my certificate expire? thank you, precious as always
@justoverclock Not necessarily. You only need to use this if it fails from the Virtualmin window
Hello! It looks like you're interested in this conversation, but you don't have an account yet.
Getting fed up of having to scroll through the same posts each visit? When you register for an account, you'll always come back to exactly where you were before, and choose to be notified of new replies (either via email, or push notification). You'll also be able to save bookmarks and upvote posts to show your appreciation to other community members.
With your input, this post could be even better 💗
Register LoginDid this solution help you?
Related Topics
-
-
SSL certificates
Solved Configure -
-
-
-
-
nginx can't start again
Moved Solved Configure -