VPN connections...
-
I usually connect to Germany or Netherlands etc. I avoid the UK connections but is that necessary?
Express VPN to give you a list of recommended connections and the top of the list is UK connection.
-
I usually connect to Germany or Netherlands etc. I avoid the UK connections but is that necessary?
Express VPN to give you a list of recommended connections and the top of the list is UK connection.
@jac The point of a VPN is not to avoid your own location, but to ensure you sit behind a secured service to ensure that your own location and IP addressed are not exposed. In most cases, you should actually choose the location closest to you for performance purposes, unless you need to use an alternative location to gain access to streaming services.
By default NordVPN and others will always choose the location that is geographically closest to you for the performance gain. In essence, no - it’s not necessary to avoid the UK connections at all. Provided the relevant security is in place, then you are good to go. For NordVPN (and probably ExpressVPN also), if you go to their website, they will tell you if you are protected or not.
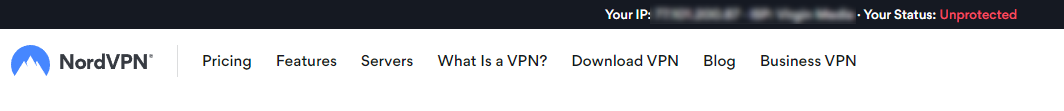
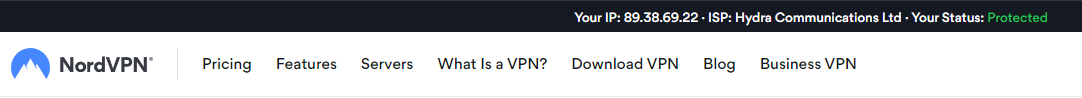
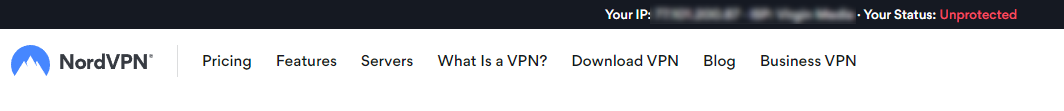
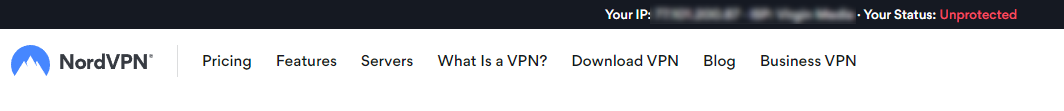
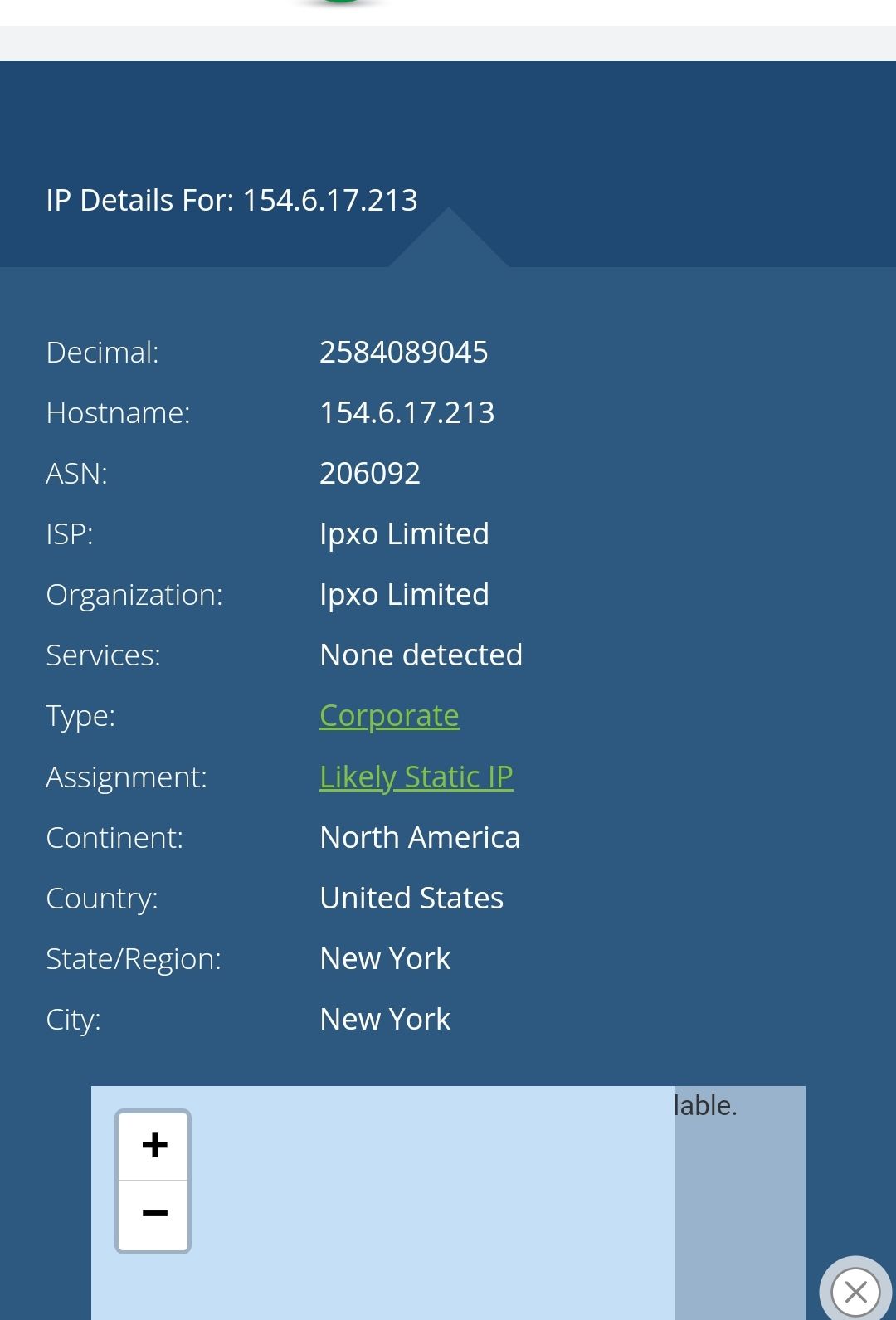
For example, an unprotected session under NordVPN looks like this
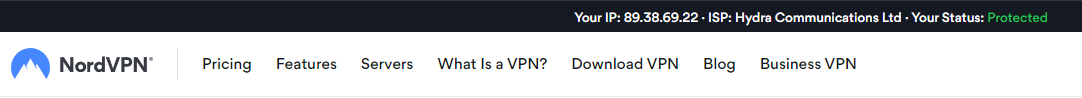
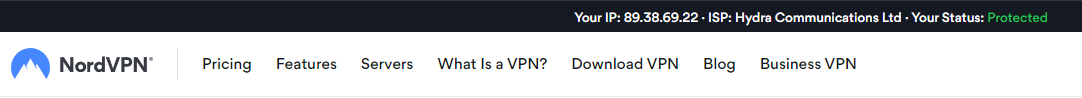
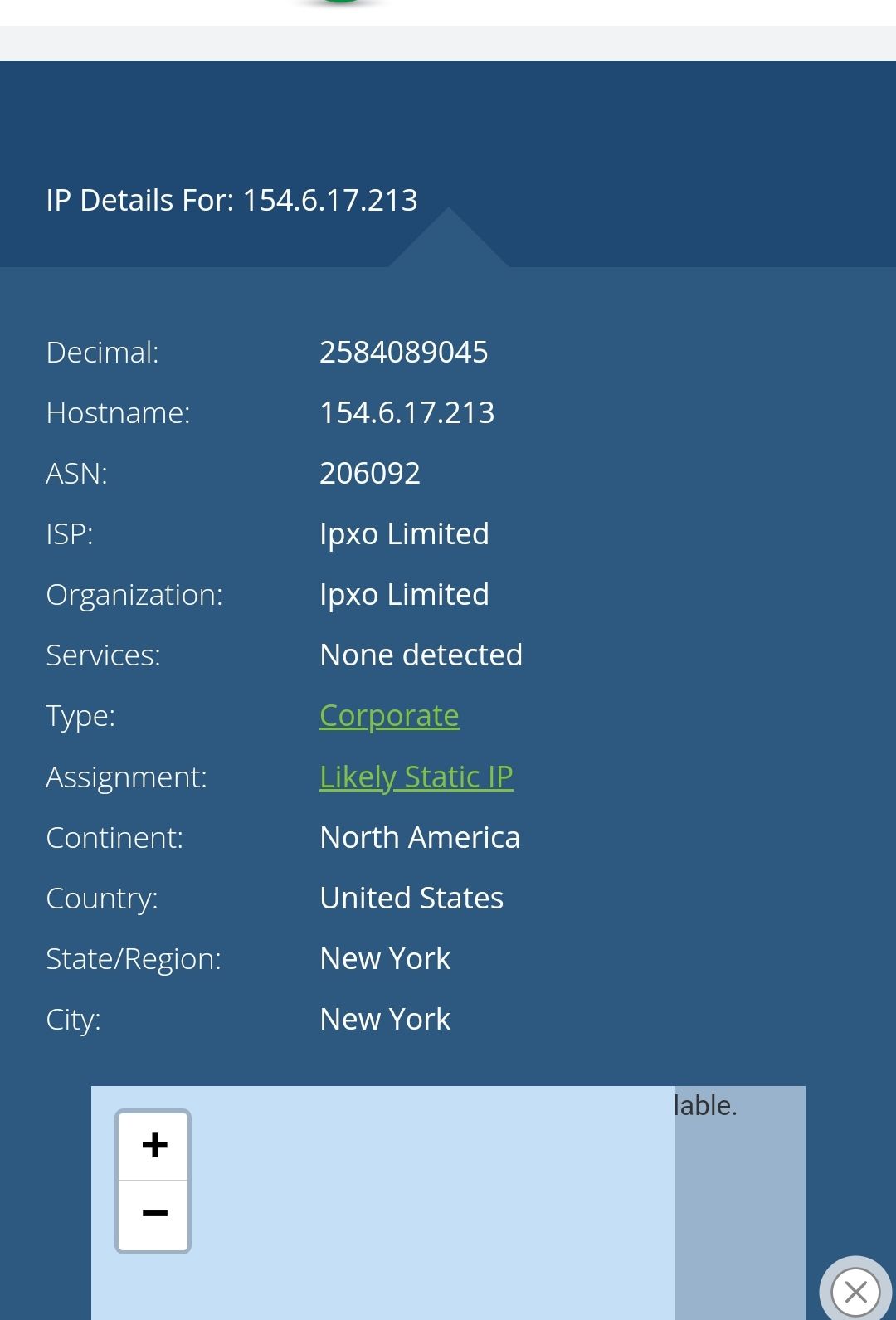
Whilst the protected session looks like this
Obviously, if you use ExpressVPN and then go to the NordVPN page, then it’ll think you are not protected as you are using another service. The best way to check is to disable the VPN, then go to
Then, re-enable the VPN, go back to the Whats My IP site, then reload the page. Your recorded IP address should have changed.
Hope this helps.
-
@jac The point of a VPN is not to avoid your own location, but to ensure you sit behind a secured service to ensure that your own location and IP addressed are not exposed. In most cases, you should actually choose the location closest to you for performance purposes, unless you need to use an alternative location to gain access to streaming services.
By default NordVPN and others will always choose the location that is geographically closest to you for the performance gain. In essence, no - it’s not necessary to avoid the UK connections at all. Provided the relevant security is in place, then you are good to go. For NordVPN (and probably ExpressVPN also), if you go to their website, they will tell you if you are protected or not.
For example, an unprotected session under NordVPN looks like this
Whilst the protected session looks like this
Obviously, if you use ExpressVPN and then go to the NordVPN page, then it’ll think you are not protected as you are using another service. The best way to check is to disable the VPN, then go to
Then, re-enable the VPN, go back to the Whats My IP site, then reload the page. Your recorded IP address should have changed.
Hope this helps.
@phenomlab said in VPN connections...:
@jac The point of a VPN is not to avoid your own location, but to ensure you sit behind a secured service to ensure that your own location and IP addressed are not exposed. In most cases, you should actually choose the location closest to you for performance purposes, unless you need to use an alternative location to gain access to streaming services.
By default NordVPN and others will always choose the location that is geographically closest to you for the performance gain. In essence, no - it’s not necessary to avoid the UK connections at all. Provided the relevant security is in place, then you are good to go. For NordVPN (and probably ExpressVPN also), if you go to their website, they will tell you if you are protected or not.
For example, an unprotected session under NordVPN looks like this
Whilst the protected session looks like this
Obviously, if you use ExpressVPN and then go to the NordVPN page, then it’ll think you are not protected as you are using another service. The best way to check is to disable the VPN, then go to
Then, re-enable the VPN, go back to the Whats My IP site, then reload the page. Your recorded IP address should have changed.
Hope this helps.
Thanks mate for that.
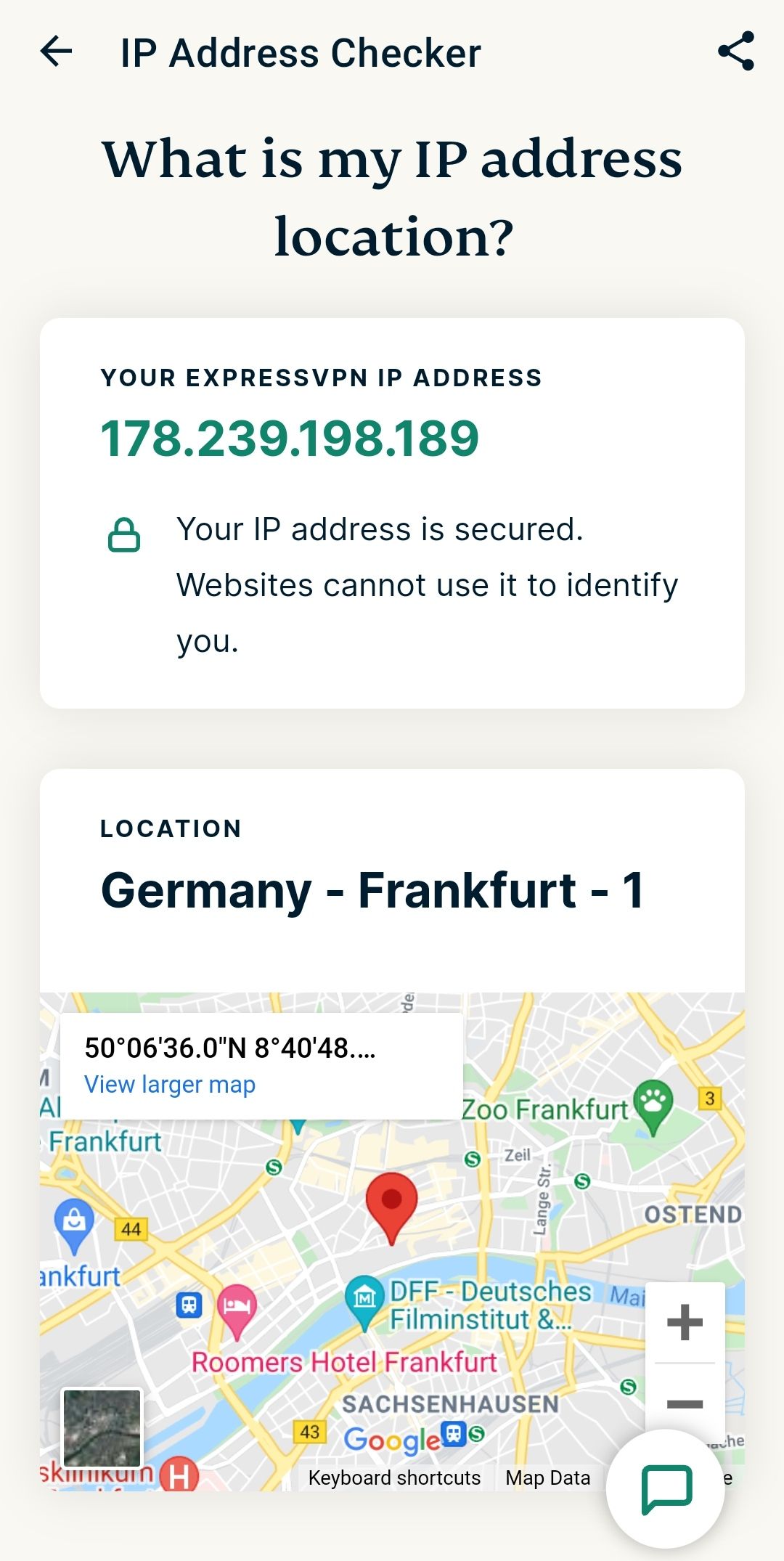
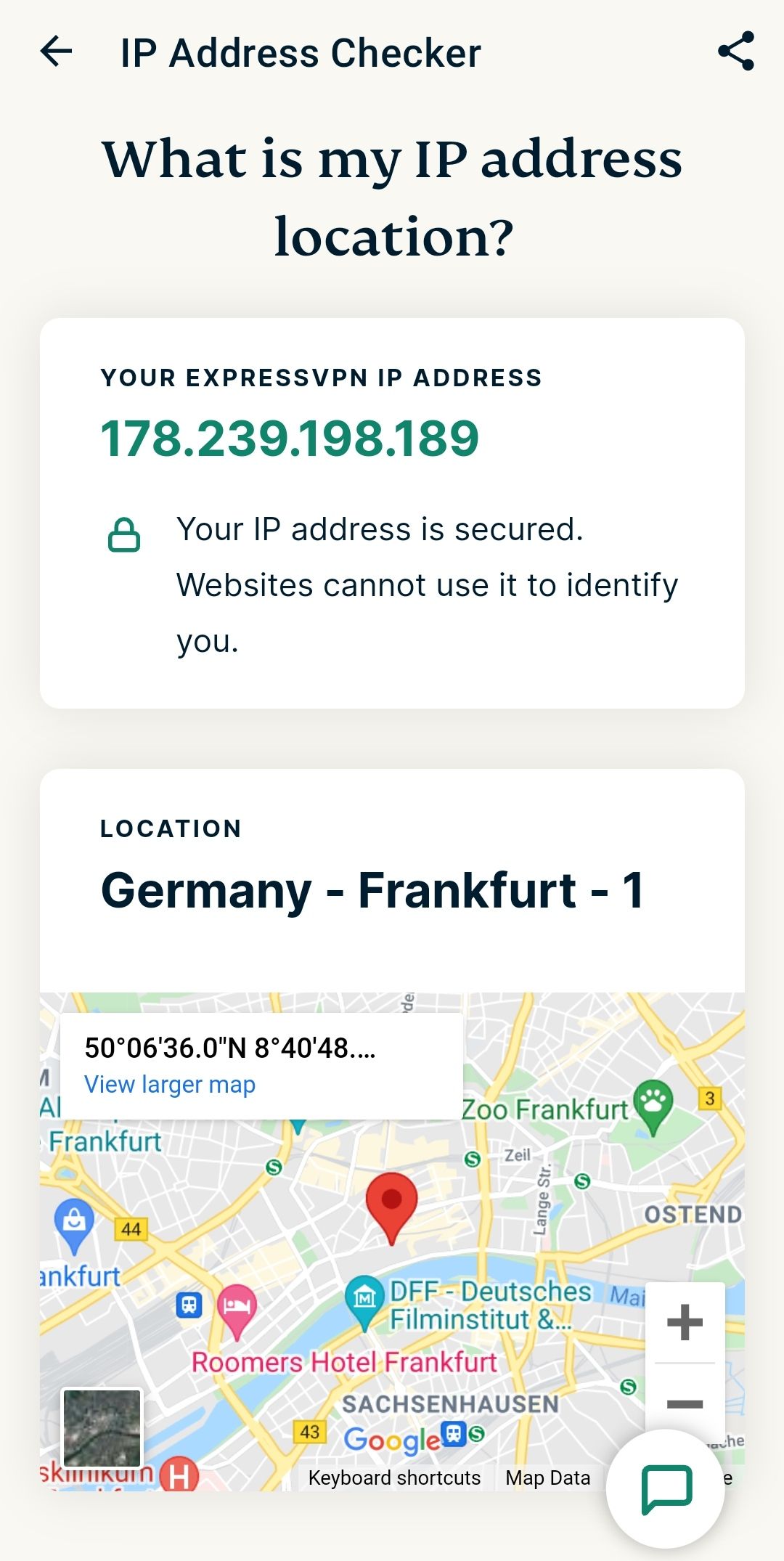
So Express VPN will show that I’m connected to Germany as below.
Despite disconnecting and reconnecting
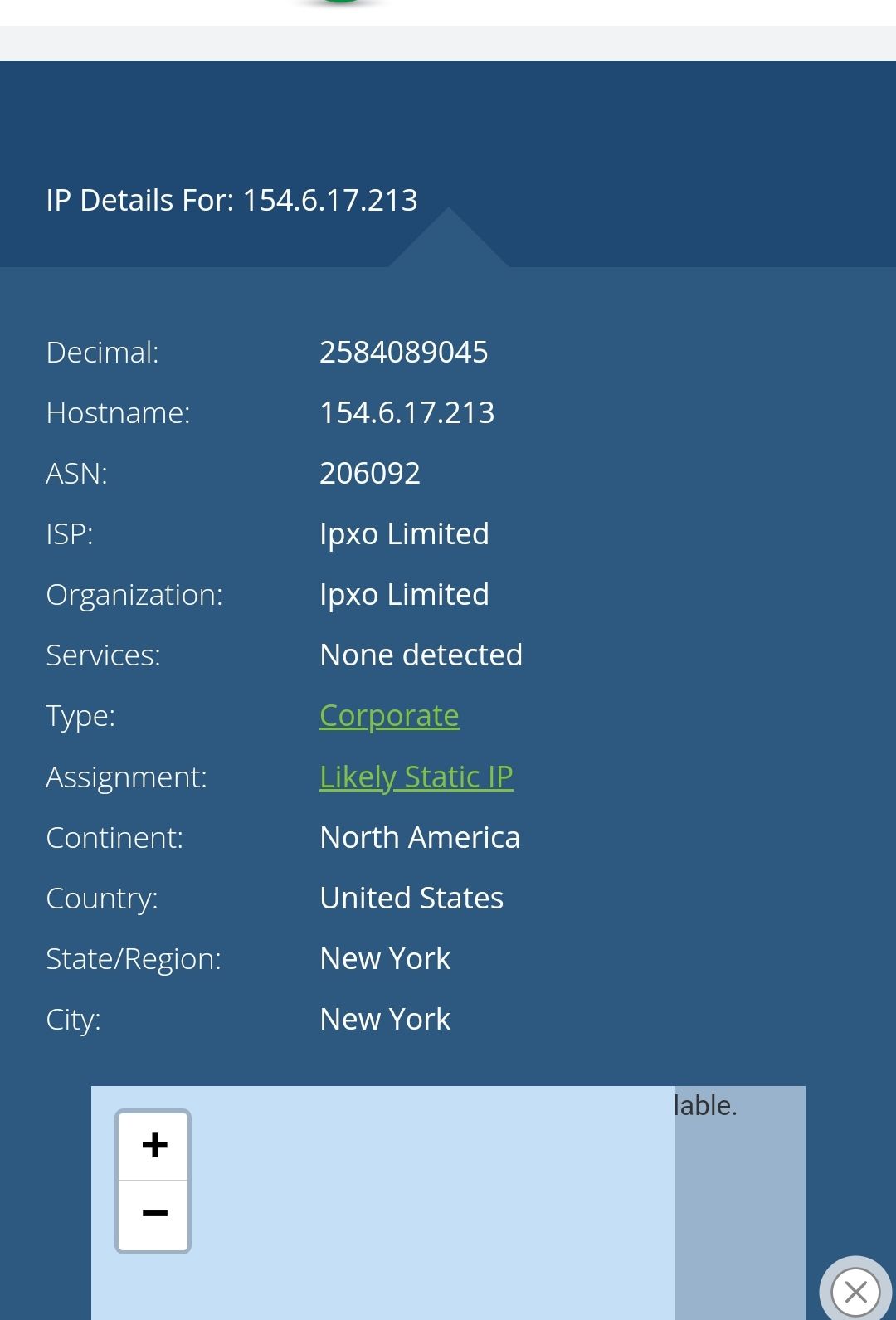
https://www.whatsmyip.org shows my actual IP address .
. -
@phenomlab said in VPN connections...:
@jac The point of a VPN is not to avoid your own location, but to ensure you sit behind a secured service to ensure that your own location and IP addressed are not exposed. In most cases, you should actually choose the location closest to you for performance purposes, unless you need to use an alternative location to gain access to streaming services.
By default NordVPN and others will always choose the location that is geographically closest to you for the performance gain. In essence, no - it’s not necessary to avoid the UK connections at all. Provided the relevant security is in place, then you are good to go. For NordVPN (and probably ExpressVPN also), if you go to their website, they will tell you if you are protected or not.
For example, an unprotected session under NordVPN looks like this
Whilst the protected session looks like this
Obviously, if you use ExpressVPN and then go to the NordVPN page, then it’ll think you are not protected as you are using another service. The best way to check is to disable the VPN, then go to
Then, re-enable the VPN, go back to the Whats My IP site, then reload the page. Your recorded IP address should have changed.
Hope this helps.
Thanks mate for that.
So Express VPN will show that I’m connected to Germany as below.
Despite disconnecting and reconnecting
https://www.whatsmyip.org shows my actual IP address .
.@jac This is worrying. The IP address should definitely change. Are you using the same browser ?
-
@jac This is worrying. The IP address should definitely change. Are you using the same browser ?
@phenomlab said in VPN connections...:
@jac This is worrying. The IP address should definitely change. Are you using the same browser ?
Duckduckgo I’m using mate. -
@phenomlab said in VPN connections...:
@jac This is worrying. The IP address should definitely change. Are you using the same browser ?
Duckduckgo I’m using mate.@jac said in VPN connections...:
@phenomlab said in VPN connections...:
@jac This is worrying. The IP address should definitely change. Are you using the same browser ?
Duckduckgo I’m using mate.Duck duck go mate.
-
@jac said in VPN connections...:
@phenomlab said in VPN connections...:
@jac This is worrying. The IP address should definitely change. Are you using the same browser ?
Duckduckgo I’m using mate.Duck duck go mate.
@jac said in VPN connections...:
@jac said in VPN connections...:
@phenomlab said in VPN connections...:
@jac This is worrying. The IP address should definitely change. Are you using the same browser ?
Duckduckgo I’m using mate.Duck duck go mate.
Chrome is showing correctly.
-
@jac said in VPN connections...:
@jac said in VPN connections...:
@phenomlab said in VPN connections...:
@jac This is worrying. The IP address should definitely change. Are you using the same browser ?
Duckduckgo I’m using mate.Duck duck go mate.
Chrome is showing correctly.
@jac said in VPN connections...:
@jac said in VPN connections...:
@jac said in VPN connections...:
@phenomlab said in VPN connections...:
@jac This is worrying. The IP address should definitely change. Are you using the same browser ?
Duckduckgo I’m using mate.Duck duck go mate.
Chrome is showing correctly.
Which is a relief

-
@jac said in VPN connections...:
@jac said in VPN connections...:
@jac said in VPN connections...:
@phenomlab said in VPN connections...:
@jac This is worrying. The IP address should definitely change. Are you using the same browser ?
Duckduckgo I’m using mate.Duck duck go mate.
Chrome is showing correctly.
Which is a relief

@jac Are you using the browser extension, or the VPN software itself ?
-
@phenomlab said in VPN connections...:
@jac Are you using the browser extension, or the VPN software itself ?
Mobile app matey.
-
@phenomlab said in VPN connections...:
@jac Are you using the browser extension, or the VPN software itself ?
Mobile app matey.
@jac Then that should be controlled at the system level. I’d expect any browser to report the correct IP in that case. Do you get the same results if you completely close DuckDuckGo and reopen then test ?
-
@phenomlab said in VPN connections...:
@jac Are you using the browser extension, or the VPN software itself ?
Mobile app matey.
@jac said in VPN connections...:
@phenomlab said in VPN connections...:
@jac Are you using the browser extension, or the VPN software itself ?
Mobile app matey.
But if you can see my different IP address here (despite duck duck go browser) then it will be working?
Which was confirmed in Chrome.
-
@jac said in VPN connections...:
@phenomlab said in VPN connections...:
@jac Are you using the browser extension, or the VPN software itself ?
Mobile app matey.
But if you can see my different IP address here (despite duck duck go browser) then it will be working?
Which was confirmed in Chrome.
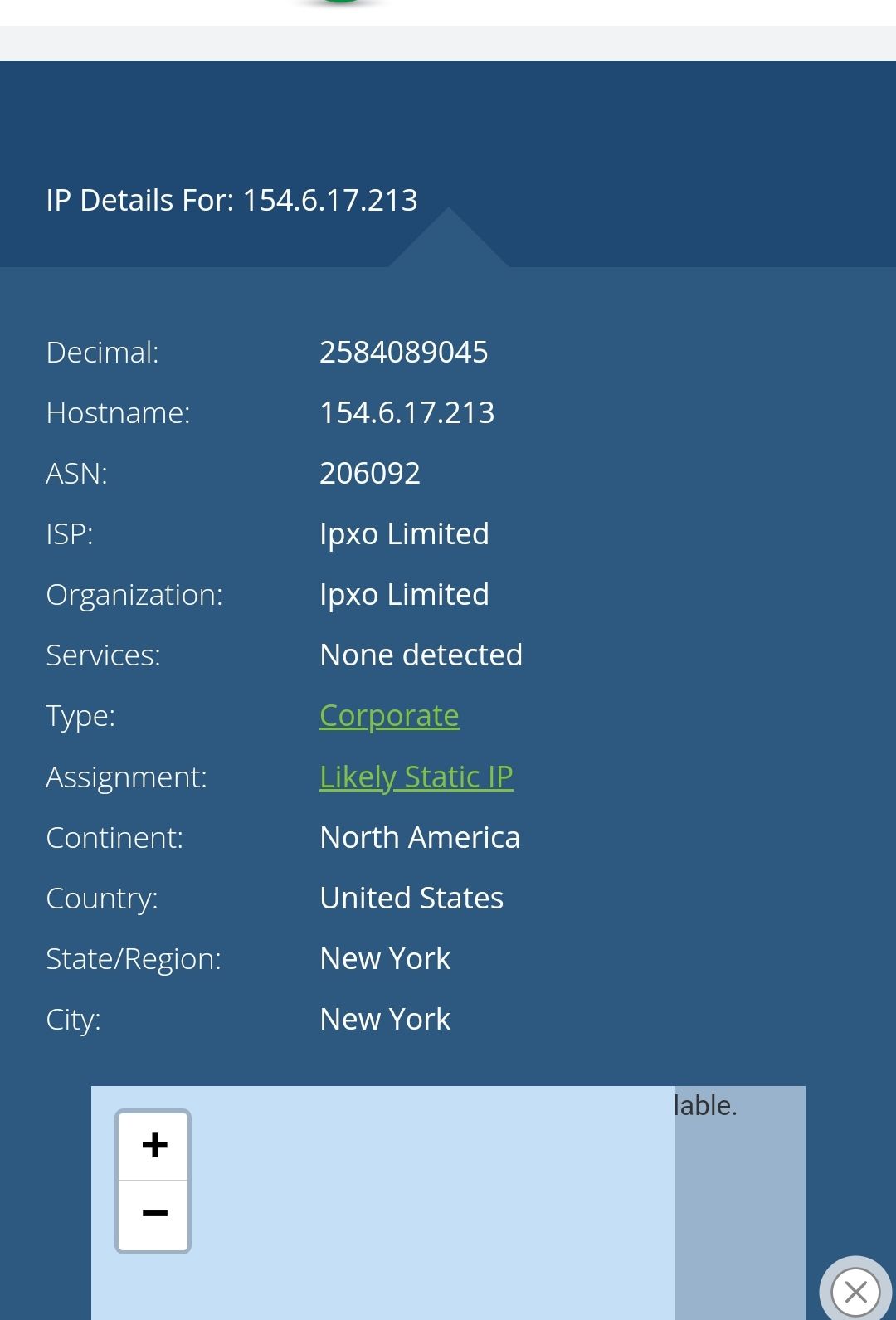
@jac No - I see your real IP

-
-
@jac said in VPN connections...:
@phenomlab said in VPN connections...:
@jac No - I see your real IP

No way!

 . Concerning.
. Concerning.I’m going to access the site in Chrome and then Brave browser, can you confirm or deny if it shows a different IP address please?
Give me a moment and I’ll test this.
-
@jac said in VPN connections...:
@phenomlab said in VPN connections...:
@jac No - I see your real IP

No way!

 . Concerning.
. Concerning.I’m going to access the site in Chrome and then Brave browser, can you confirm or deny if it shows a different IP address please?
Give me a moment and I’ll test this.
@jac Sure
-
@phenomlab said in VPN connections...:
@jac Sure
Thanks mate. I have just accessed the site in two separate browsers with different actions.
I didn’t login with either browser, hopefully that doesn’t effect the result.
-
@phenomlab said in VPN connections...:
@jac Sure
Thanks mate. I have just accessed the site in two separate browsers with different actions.
I didn’t login with either browser, hopefully that doesn’t effect the result.
@jac I still see the same IP address mate. Contact me in PM to confirm if this is actually your real IP or one you’ve been granted via the VPN
-
@JAC On checking, I actually get the same. You have to logout of Sudonix completely, then back in otherwise it just uses the existing session - regardless if you use another browser.
I tested this, and it’s using my actual IP. As soon as I logged out and back in again, it uses the VPN IP
-
@JAC On checking, I actually get the same. You have to logout of Sudonix completely, then back in otherwise it just uses the existing session - regardless if you use another browser.
I tested this, and it’s using my actual IP. As soon as I logged out and back in again, it uses the VPN IP
@phenomlab said in VPN connections...:
@JAC On checking, I actually get the same. You have to logout of Sudonix completely, then back in otherwise it just uses the existing session - regardless if you use another browser.
I tested this, and it’s using my actual IP. As soon as I logged out and back in again, it uses the VPN IP
Logged in now Mark via Brave browser…
Hello! It looks like you're interested in this conversation, but you don't have an account yet.
Getting fed up of having to scroll through the same posts each visit? When you register for an account, you'll always come back to exactly where you were before, and choose to be notified of new replies (either via email, or push notification). You'll also be able to save bookmarks and upvote posts to show your appreciation to other community members.
With your input, this post could be even better 💗
Register Login